Australian Member of Parliament’s Websites: How Secure Are They?

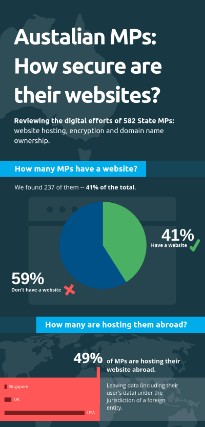 The 2019 federal elections are just around the corner, so we thought it would be an interesting exercise to review Australian Member of Parliament websites and see how they perform against a relatively simple security and best practices check.
The 2019 federal elections are just around the corner, so we thought it would be an interesting exercise to review Australian Member of Parliament websites and see how they perform against a relatively simple security and best practices check.
Bear in mind that this wasn’t a comprehensive analysis but more of a general overview. If we repeat the same checks now results may well be different. Hopefully better.
As part of the process, we emailed MPs to let them know of our findings and gave them plenty of time to make changes. We put together a PDF covering best practices and included a checklist for them to share with their web developers.
View infographic on LinkedIn, Twitter or Facebook
Researching the websites of 582 MPs
In January 2019, we researched publicly available data from portals such as Parliament of Victoria and Queensland Parliament, making a note of email addresses and URLs of personal websites. If the latter were not listed we tried to find them via Google.
Initial Findings
We got our first statistic of relevance at the end of this process: of the 582 MPs we researched, 237 of them had websites, so 41% of the total.
Areas of Focus in Our Research
So, with our original list cut in half we checked the following:
- Hosting – what company was used and in what country their servers are located
- SSL Certificates – whether any were installed and if so, whether there were any errors
- Domain registration – checking the details for the Registrant Contact Name and Registrant Contact Email specifically
- Performance – using GT Metrix to check homepages size and page load times, taking the average of three checks for accuracy
What We Didn’t Check
We didn’t look at what applications were hosted nor the technical specs of the hosting providers. We also didn’t conduct any vulnerability or penetration testing, as we’ve seen on many public-facing Government websites and applications.
Our findings
1. Hosting
Of the 237 websites, we looked at 49% (115) were hosted abroad. While many Australian businesses host their websites abroad – we don’t think MPs should be doing so:
- They are hosting their data, and potentially data of Australian citizens, with companies that don’t have to comply with Australian legislation
- Foreign companies or authorities may have full access to this data
- There are web hosting providers here in Australia that, just like us, offer a great product, local support and comply with Australian laws
In regards to the above, the Australian Cyber Security Center recently published a Cloud Computing Security Considerations document covering this scenario specifically:
The ACSC recommends against outsourcing information technology services and functions outside of Australia, unless organisations are dealing with data that is all publicly available. The ACSC strongly encourages organisations to choose either a locally-owned vendor or a foreign-owned vendor that is located in Australia and stores, processes and manages sensitive data only within Australian borders. Note that foreign-owned vendors operating in Australia may be subject to foreign laws such as a foreign government’s lawful access to data held by the vendor.
2. Securing communication with SSL
SSL certificates encrypt data as it travels to and from a user’s browser. For example, login details, credit card information and enquiries passed via online forms.
While we didn’t see any form or website function capturing critical data such as credit card numbers we wouldn’t want anyone intercepting our personal information such as our name, phone number and email address.
13% of the websites we analysed either had no SSL certificate in place or it wasn’t installed correctly. That’s 31 out of 237 websites that are at risk of ‘leaking’ data as users interact with them.
There is no excuse for failing to install an SSL certificate considering you can get them for free from most web hosting providers. In fact, of those that do have SSL in place, 133 use a free version.
Free SSL certificates are good enough for the type of functions you find on websites that are mostly informational, however, premium versions that come with installation support and warranties typically cost less than $50 a year.
3. Domain registration
We recommend that our customers always use their own details when they sign up for services, including domain registration. If not, they risk losing access to those services, or even worse, someone taking over and using them maliciously.
36% of MPs domain names list third parties as the Registrant contact. In most cases, these are the web developers or agencies that have built their websites. This means any administrative or renewal emails related to the domain could be overlooked and not forwarded to the domain owner.
The Importance of Proper Domain Management
Premier Scott Morrison was lucky when a prankster registered his expired domain. He just wanted to have a little fun. Someone else could have pointed the domain to somewhere malicious or spoofed his site to capture personal data and send misleading information.
AuDA states “It is necessary for the WHOIS data to include a contact email address for the registrant, for the purpose of contacting the registrant in relation to their domain name. The registrant does not have to nominate their own personal email address, but they must nominate an email address at which they can be contacted.”
As a domain name is the cornerstone of a website, proper management of this digital asset is critical. Assigning domain management to a third party or unmonitored email account could end in disaster.
4. Performance
Results were in line with the norm with page load speeds averaging 5.8 seconds and an average page size of 3.4MB.
If you’re running an eCommerce store or transactional-based website you will want to boost those figures though, as research shows that visitors tend to drop off in droves if you make them wait any longer than 2 seconds.
MPs publish mostly information about their policies and achievements, so it’s not hard to keep the interface light, page load times low and offer a better user experience. The load time averages are likely higher due to the number of websites hosted overseas on commodity hosting solutions.
Sharing our results with MPs
This proved to be much harder than expected. MPs and their teams must be busy these days and their email autoresponders often said the same thing:
That said, we approached them with some urgency and were able to share informative data relevant to their websites, as well as tips on how to best manage hosting, domains, and digital security.
The sequence was as follows:
22nd February 2019 – First email, sent to all MPs – with versions for those with a website and those without to raise awareness.
Bounced emails: 3.4% (20)
Opens: 25.2% (148)
Human Replies: 0.5% (3)
3rd March 2019 – Follow up sent to all MPs – minus the ones that bounced or indicated that they didn’t want to hear from us anymore.
Bounced emails: 1.3% (7)
Opens: 32.6% (182)
Human Replies: 0.7% (4)
What’s interesting here is that these stats are in line with what you would expect from your typical email newsletter. But looking at the open rates, shouldn’t they be closer to 100%? Surely MPs have staff that check every piece of communication they receive before deciding whether to reply or not?
Results by party
To determine this we flagged all MPs experiencing at least one of the three issues we looked at: hosting their website abroad, not having a properly configured SSL certificate in place or not owning the domain’s Registrant Name and Email details.
The results were…
| Total MP Websites | Websites with issues | Percentage with issues | |
| Labour | 87 | 56 | 64.4% |
| Liberals | 102 | 88 | 86.3% |
| Green | 12 | 9 | 75.0% |
| Other | 36 | 26 | 72.2% |
Of the three main parties Labour performed best, but the with more than half of their websites ‘offending’ they have a lot of work to do too.
Concerns with US-Based Hosting
Many of the websites are published on the Nation Builder platform, which is owned by US-based 3dna, Corp. They host customers in US-based data centres, including content, files and customer data of Australian MPs using their service.
3dna, Corp. is based in California and therefore abiding by local rules and regulations governing access to their data, and our MPs are effectively disregarding ASCS’s recommendation to store sensitive data within our borders.
Digital best practices: another thing we can accuse our politicians to underdeliver on?
It goes without saying that MPs websites should be leading by example as far as security and user experience is concerned.
They (their staff, at least) should make more of an effort to use local tech and talent too. They should at least glance over all their emails and contract reputable web developers that can advise them on best practices.
Concluding thoughts: our MPs may be putting their websites and data at risk!
This simple exercise has shown us that 76% of MP’s websites we looked at didn’t pass our security and best practices check. If you suspect your local MP is not following best practices, point them to this article.
The Australian Cyber Security Centre is there to remind us too and help us keep safe. We share their mission to make Australia the safest place to connect online.